It’s been circulating for more than a decade, but now ransomware is becoming an increasing problem for businesses of all sizes.
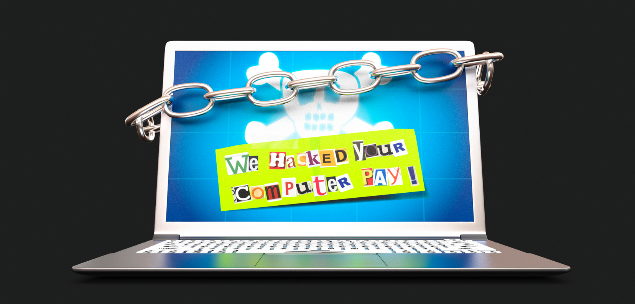
Designed for financial gain, ransomware attacks involve malicious code that infiltrates a victim’s computer or a company’s server infrastructure and encrypts stored data. The first a victim knows of the attack is when a message appears demanding a ransom payment in exchange for the decryption code.
One of the most high-profile ransomware attacks was Cryptolocker that appeared during 2013. While it wasn’t the first of its type, its success attracted considerable media and public attention. According to industry estimates, the CryptoLocker malware authors collected around $US27 million from their victims during the first three months.
In 2014, CryptoLocker was effectively neutralised by Operation Tovar, an international collaboration of security companies and law enforcement agencies. The major operation managed to shut down the command-and-control servers that were driving the ransomware attacks, bringing an end to the malicious code’s ability to infect and encrypt systems.
The problem continues
However, despite the success of Operation Tovar, it did not spell the end of the ransomware threat. Since then, new variants have continued to appear and cause disruption and loss for both consumers and businesses around the world.
There are a number of reasons why attacks are becoming more successful. As the required computer code can be readily sourced from a range of locations on the internet, perpetrators need malicious intent but don’t need any coding skills. Also, digital mechanisms such as Bitcoin allow payments to be collected anonymously with little or no potential for tracking. This makes collection of ransom payments much more straightforward.
According to the PwC Global State of Information Security 2016, there were 38 per cent more security incidents in 2015 compared with the previous 12 months. Yet many security experts fear the problem could be even more widespread. Ransomware is not a data breach as data is not extracted but encrypted on the target devices. As a result, attacks may go unreported as the regulations that require disclosure of data breaches are not triggered.
Second generation
As criminals continue to work on improving their ransomware tools, new generations are emerging. A worthy successor to CryptoLocker was CryptoWall which has evolved into one of the nastiest and most successful strains of ransomware yet seen.
It has been known to arrive via email attachments, exploit kits and drive-by downloads that occur when a user unintentionally downloads a virus or malware due to having an outdated browser or a lack of proper end point security.
The latest version of this threat, dubbed CryptoWall version 3, is much more complex than its predecessors. More than 4,000 different variants of the code have been discovered in the wild and it uses more than 800 different command-and-control URLs for communication.
Security experts estimate there have already been more than 400,000 attempted infections and the criminals behind it collected an estimated $US325 million via Bitcoin during 2015.
Earlier this year, a new version called Locky appeared. This code has a similar payload to CryptoWall but was targeted specifically at healthcare organisations. In February, the US-based Hollywood Presbyterian Medical Centre fell victim to the code and was forced to pay about $US17,000 to regain access to encrypted medical files.
The evolving threat landscape
The ransomware threat is showing no sign of slowing. According to research firm Gartner, 60 per cent of the Alexa top 100 internet sites have some sort of malware that could trigger a ransomware event. It might not be the site itself that is infected but could be an element supplied by a third party such as an advertising company.
Another challenge is caused by the fact that around 40 per cent of internet traffic now crosses Content Delivery Networks (CDNs) and therefore often goes uninspected. Security solutions tend to make a lot of reputation-based scanning decisions and trust CDNs – this is becoming a mistake.
Yet another challenge, according to ThreatLabz Research, is that 54 per cent of advanced threats now hide behind SSL encryption. Many organisations have no ability to scan this type of traffic and so threats can go unnoticed.
Future challenges
Based on current trends, the focus of ransomware criminals will continue to shift from individuals to large organisations and businesses. A key reason is that these targets have a greater ability to pay and potentially more to lose. Evidence shows the average ransomware bill for a large organisation is now around $US5000 compared with consumer victims who tend to have to pay around $US600.
Security teams are also seeing ransomware variants that infiltrate an organisation’s network but don’t immediately encrypt data. Instead, the attackers take time to identify high-value servers and figure out back-up strategies so the eventual impact can be even more significant.
One variant, called Maktub, even uses a time-sensitive ransom note. If the requested ransom is not payed within 15 days, the price goes up.
Security strategies
It’s becoming increasingly clear that traditional security solutions are no longer up to the task when it comes to protecting organisations against ransomware. Growing usage of mobile devices and cloud-based applications and services means users are not protected, and internet gateways are unable to handle advanced threats.
A solution is to adopt a cloud-based security platform which removes complexity from within the organisation and ensures comprehensive protection. Cloud-based services build a perimeter around all users regardless of their location and endpoint device. All traffic is directed through the cloud where it is scanned and analysed before going to the internet.
This approach consolidates and simplifies point appliances and provides comprehensive protection. It includes everything from firewall and URL filtering to intrusion prevention and advanced protection. The platform can also provide sandboxing which takes malware that has never before been seen and tests it before allowing it into the organisation’s infrastructure.
By shifting to a cloud-based protection architecture, organisations will be much better placed to avoid the disruption and potential cost of a ransomware attack.
About the author
Scott Robertson is the Vice President of cloud-based security company Zscaler for the Asia Pacific.